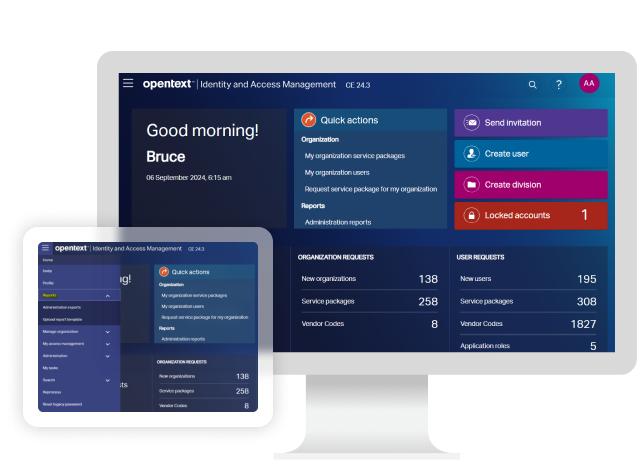
OpenText Core Secure Access
Strengthen supply chain security with secure access
IDC MarketScape names OpenText a 4x Leader in MESCCNGet the IDC excerpt
Complete supply chain collaboration
Organizations face increasing threats from supply chain security risks. Gain peace of mind with a robust, scalable solution for seamlessly managing external user identities and access across enterprise ecosystems.
OpenText™ Core Secure Access mitigates supply chain security risks using a zero-trust framework, automating third-party onboarding and enabling real-time monitoring of access rights and permissions. Its scalable architecture secures access for every trading partner relationship, regardless of IT footprint, systems, and user experience requirements, so businesses can securely manage their supply chain and prevent unauthorized access to systems.
Why OpenText Core Secure Access?
Achieve secure collaboration across your business ecosystem with a trusted identity and access management (IAM) solution designed to reduce supply chain risk, automate compliance, and improve operational efficiency.
- 93%
fewer breaches
Reduce supply chain risk by applying zero-trust policies to external partners and suppliers. - 50%
faster workflows
Use automation to simplify supplier lifecycle management, reduce manual processes, and improve compliance. - $4.35M
in breach costs avoided
Implement proactive security measures that protect against costly breaches by ensuring continuous identity verification and governance.
Use cases
Organizations need a scalable and secure access solution to mitigate supply chain risk, manage third-party relationships, and enforce compliance policies. OpenText Core Secure Access ensures safe, efficient, and automated access management at scale.
-
Strengthen access control by validating user identities in real time and using risk-based authentication to minimize vulnerabilities from third-party access.
-
Streamline supplier access by using automated workflows and self-service portals to quickly and securely grant appropriate access levels.
-
Protect critical systems by applying least-privilege principles, continuously verifying identities, and adapting access based on contextual risk.
-
Maintain a single connection to the IAM platform to reduce exposed endpoints and the attack surface.
-
Increase operational maturity and risk posture with a common, digital approach to onboard, manage, and offboard third-party organizations and users.
-
Securely authenticate users and share identity information with applications and systems more easily to ensure cross-organization collaboration.
Key features
OpenText Core Secure Access ensures enterprise-grade supply chain security, enabling secure access across unknown environments without compromising user experience, while enforcing zero-trust principles.

Identity-centric security
Enforces least-privilege access policies that reduce supply chain exposure and limit unauthorized access.

Third-party onboarding automation
Streamlines supplier registration and verification to accelerate onboarding and minimize manual intervention and delivers unified, seamless experiences.

Centralized access governance
Provides real-time visibility and control over user permissions to ensure policy enforcement, compliance monitoring, and audit readiness.

Adaptive, low-friction authentication
Uses risk-based authentication (RBA), adaptive, multi-factor authentication (MFA), FIDO U2F, token verification, and more to adapt authentication security based on real-time risk evaluations.

Identity-driven user experiences
Dynamically controls what each user can view, select, and request based on their authorizations, profile, preferences, relationships, external API calls, and other data.

IAM Platform as a Service
Offers an API-first, auto-scaling micro services architecture to rapidly develop applications and custom IAM solutions within a DevSecOps environment.
Accelerate the value of OpenText Core Secure Access
Deployment
Explore scalable and flexible deployment options for global organizations of any size.
Services
Accelerate digital transformation with guidance from certified experts.
-
Modernize your information management with certified experts
Professional Services
-
Turn support into your strategic advantage
Support Services
-
Meet business goals with expert guidance, managed services, and more
Customer Success Services
-
Free up your internal teams with expert IT service management
Managed Services
Training
OpenText Learning Services offers comprehensive enablement and learning programs to accelerate knowledge and skills. Empower your team with flexible, expert-led training to master OpenText solutions and drive success.
Communities
Explore our OpenText communities. Connect with individuals and companies to get insight and support. Get involved in the discussion.
OpenText Core Secure Access resources

Explore why IDC MarketScape named OpenText a Leader in the worldwide Multi-Enterprise Supply Chain Commerce Network (MESCCN) category. The report highlights OpenText’s strengths in end-to-end B2B integration, secure partner collaboration, real-time visibility, and scalable supply chain automation. Learn how these capabilities help organizations reduce friction across partner ecosystems, improve operational resilience, and modernize supply chain collaboration at scale.
Drive growth by automating third-party access to enterprise information at scale
Read the white paperFix hidden supply chain issues with automation, visibility, and collaboration
Read the ebookStreamline supplier collaboration with secure, scalable, cloud-based access
Read the solution overviewFix hidden supply chain issues with automation, visibility, and collaboration
Read the ebookStreamline supplier collaboration with secure, scalable, cloud-based access
Read the solution overview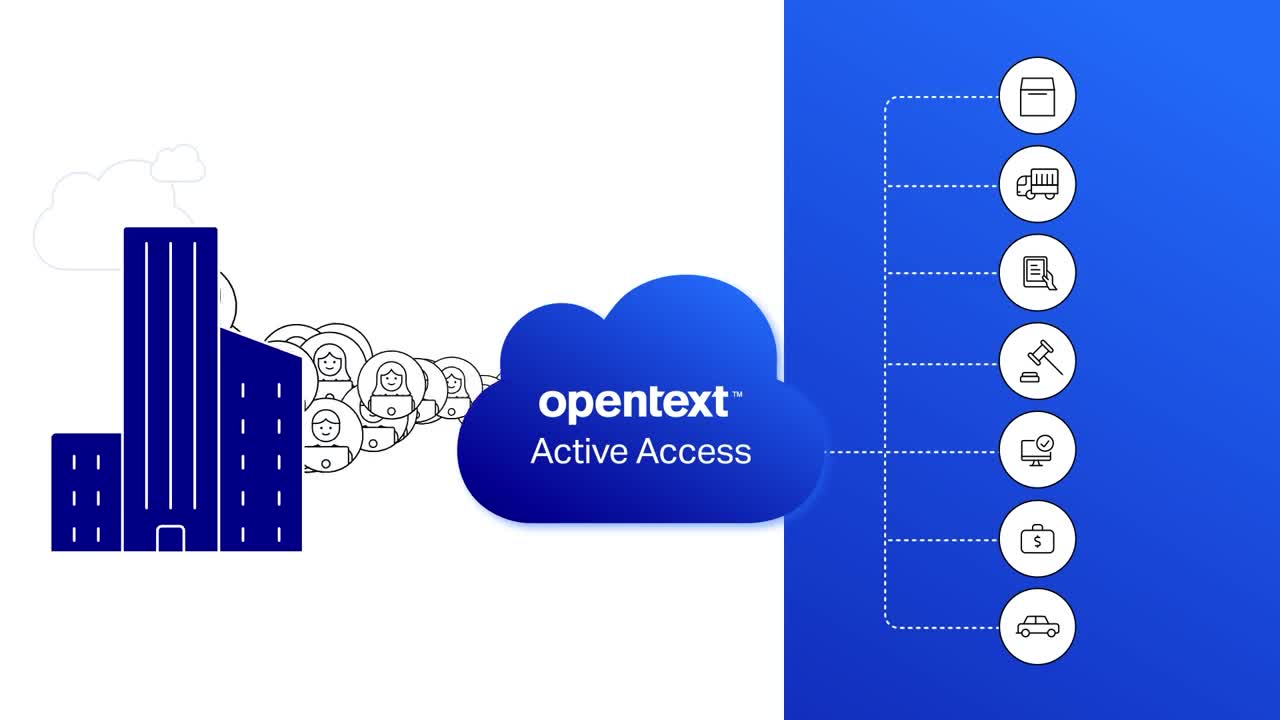
Learn how to securely build, manage, and connect ecosystems at scale with OpenText
Watch the video
Better customer experience via identity and access management at The Auto Club Group
Watch the video
Leverage IAM innovations to scale security enterprise-wide
Watch the video-
OpenText Core Secure Access is a cloud-based platform that delivers enterprise-class security for the extended partner ecosystem, enabling secure access across collaborative business application environments without compromising user experience.
-
It accelerates and standardizes third-party onboarding through self-paced, workflow-driven processes and comprehensive self-service capabilities, minimizing onboarding costs and delays.
-
It supports multiple authentication options, including risk-based authentication (RBA), MFA, FIDO U2F, phone, push, and mobile authenticator.

8 Benefits of leveraging the digital supply chain
Unlock 8 key benefits of digital supply chains for smarter, faster business.
Read the blog
4 Strategies to overcome supply chain collaboration challenges
4 smart strategies to boost supply chain collaboration and cut complexity.
Read the blog
Scale your digital ecosystem with secure access management
Enable secure, enterprise access to digital ecosystems at scale.
Read the blog
Take the next step






