OpenText Core Behavioral Signals
Detect insider threats and behavioral anomalies in real time with UEBA
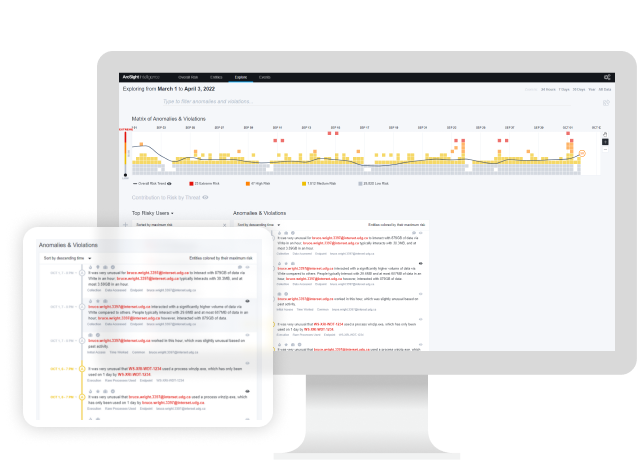
Behavioral threat detection and insider risk detection
Insider threats, both intentional and through negligence, can lead to huge losses. Organizational infrastructures and cybersecurity environments have become so complex that detecting insider threats is very time consuming.

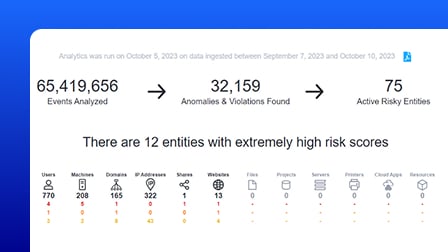
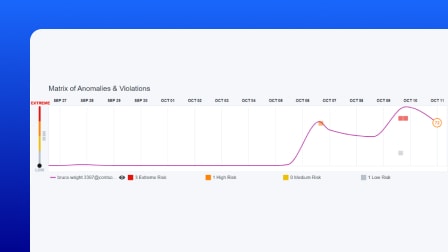
OpenText™ Core Behavioral Signals is a behavioral analytics solution that uses unsupervised machine learning and UEBA cybersecurity to identify hidden threats within your organization. It automatically adapts to your environment, detects anomalous behavior, and helps threat hunters and security analysts act faster by surfacing the most relevant leads—no rule writing required.
Why OpenText Core Behavioral Signals?
OpenText Core Behavioral Signals uses AI to detect behavioral anomalies in real time, helping security teams uncover advanced threats, reduce alert noise, and cut investigation time.
- 24/7
always-on detection for insider threats
Detect risky activity and advanced threats without relying on rules, thresholds, or signatures—even when tactics change. - 100%
fully unsupervised machine learning
Behavioral baselines adapt automatically over time, eliminating the need for manual tuning or retraining models. - Billions
of events analyzed, a handful of leads provided
Surface meaningful threat leads by filtering signal from noise—no matter how much data you’re working with.
Use cases
From insider risks to compromised credentials, OpenText Core Behavioral Signals provides threat hunting tools that reveal hard-to-detect threats through behavioral insights.
-
Identify employees or contractors behaving out of character—before data exfiltration or sabotage occurs. Behavioral baselines adapt in near real time to flag risky deviations.
-
Spot threats that don’t match known IOCs or signatures. Behavior-based detection uncovers novel attack techniques before they escalate.
-
Filter out the noise and get high-priority leads. OpenText Core Behavioral Signals surfaces real threats with rich context, reducing analyst workload.
-
Detect stolen credentials through behavior anomalies like unusual login times, privilege changes, or lateral movement—without creating rules.
-
Uncover low-and-slow threats by spotting changes in behavior of previously quiet accounts. This tactic is essential for detecting long-dwell intrusions.
-
Catch suspicious access to sensitive data and IP—before it’s leaked or shared. Behavioral context helps stop accidental or malicious misuse quickly.
Key features
Surface real risks faster using behavioral analytics, UEBA, and unsupervised machine learning—no tuning or rule-writing required.
Behavioral anomaly detection
Continuously monitors user and entity behavior to uncover suspicious activity, even when threats evolve or mimic normal behavior.
Unsupervised machine learning engine
Learns normal behavior patterns from your data automatically—no need for labeled data or manual rule creation.
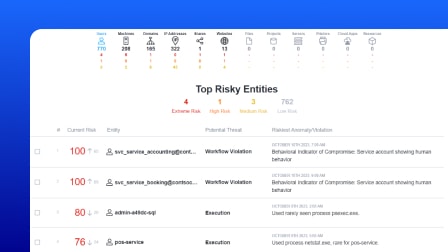
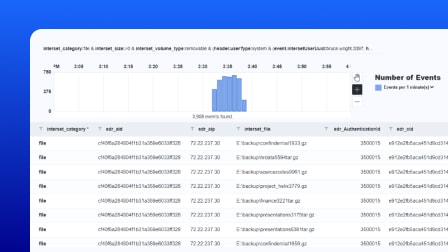
Risk-based lead generation
Transforms raw logs into prioritized threat leads by identifying behavior that deviates significantly from the norm.
Reduced response time
Helps threat hunters move quickly by surfacing enriched leads that reduce investigation time and cognitive overload.
How to buy
OpenText Core Behavioral Signals
| Organizational risk at a glance |
|---|
| Dynamic anomaly and risk timelines |
| Fully transparent alerts |
| Analyst collaboration |
| MITRE ATT&CK mapping |
| Raw events viewer |
| APIs for SOAR and trouble ticketing system |
| CrowdStrike Falcon data support |
| Public cloud |
|---|
Accelerate the value of OpenText Core Behavioral Signals
Services
Accelerate digital transformation with guidance from certified experts.
-
Modernize your information management with certified experts
Professional Services
-
Turn support into your strategic advantage
Support Services
-
Meet business goals with expert guidance, managed services, and more
Customer Success Services
-
Free up your internal teams with expert IT service management
Managed Services
Partners
OpenText helps customers find the right solution, the right support, and the right outcome.
-
Search OpenText's Partner directory
Find a Partner
-
Explore OpenText's Partner solutions catalog
Application Marketplace
-
Industry-leading organizations that enhance OpenText products and solutions
Strategic Partners
Training
Learning Services offers comprehensive enablement and learning programs to accelerate knowledge and skills.
-
Meet the demands of all types of users for effective adoption
Learning Services
-
Get expertise as needed
Flexible Credits
Communities
Explore our OpenText communities. Connect with individuals and companies to get insight and support. Get involved in the discussion.
-
Explore and vote on ideas, participate in the forums, and network with your peers
OpenText Enterprise Cybersecurity Community
-
Expert insights, threat intel, and product updates—built for SMBs
OpenText Cybersecurity SMB Community
Premium Support
Optimize the value of your OpenText solution with dedicated experts who provide mission-critical support for your complex IT environment.
OpenText Core Behavioral Signals resources
ArcSight Intelligence Behavioral Analytics
Learn moreArcSight Intelligence Threat Hunting
Learn moreArcSight Intelligence with Microsoft Defender for Endpoint
Learn moreArcSight for preemptive threat detection
Learn moreWhat is User and Entity Behavior Analytics (UEBA)?
Learn moreWhat makes ArcSight Intelligence different part 1
Read the position paperWhat makes ArcSight Intelligence different part 2
Read the position paperArcSight Intelligence Threat Hunting
Learn moreArcSight Intelligence with Microsoft Defender for Endpoint
Learn moreArcSight for preemptive threat detection
Learn moreWhat is User and Entity Behavior Analytics (UEBA)?
Learn moreWhat makes ArcSight Intelligence different part 1
Read the position paperWhat makes ArcSight Intelligence different part 2
Read the position paper
Insider threats in cybersecurity: When danger comes from within
Explore the complex issue of insider threats. From 3rd party risks to phishing and ransomware.
Read the blog
Select the right cybersecurity AI tools with these 3 crucial steps
Can AI really help you with your cybersecurity? Yes if you choose the right tools. Learn how.
Read the blog
Take the next step










